-
Posts
159 -
Joined
-
Last visited
-
Days Won
7
Content Type
Profiles
Forums
Downloads
Gallery
Everything posted by saiaapiz
-
View File Double-Click UI Toggle your cheats, function, var just by Double-Clicking GG Icon ! Submitter saiaapiz Submitted 12/21/2019 Category Templates
-
-
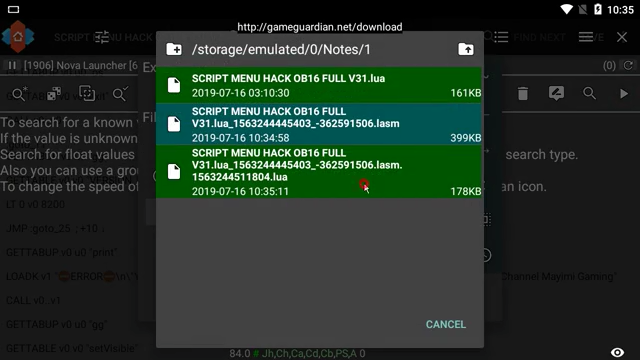
View File Call Of Duty: Mobile Cheats ! Features :- - Wallhack - Radar - Distance ESP - Aimlock - No Recoil - No Spread - Instant Fire - Much more coming soon ! How to use :- - Execute aPizClient. - Use 'freemium' as username. - Select xCODM. - Toggle your desire cheats, and enjoy ! Note : - - Make sure you hide GG to prevent from getting banned ! - This script will outdated in 3 days ! For more information, checkout http://t.me/apizhax ! Gameplay :- Submitter saiaapiz Submitted 11/19/2019 Category LUA scripts
-
Version 1.0.0
66,169 downloads
Features :- - Wallhack - Radar - Distance ESP - Aimlock - No Recoil - No Spread - Instant Fire - Much more coming soon ! How to use :- - Execute aPizClient. - Use 'freemium' as username. - Select xCODM. - Toggle your desire cheats, and enjoy ! Note : - - Make sure you hide GG to prevent from getting banned ! - This script will outdated in 3 days ! For more information, checkout http://t.me/apizhax ! Gameplay :- -
Maybe this would be useful, function rwmem(Address, SizeOrBuffer) assert(Address ~= nil, "[rwmem]: error, provided address is nil.") _rw = {} if type(SizeOrBuffer) == "number" then _ = "" for _ = 1, SizeOrBuffer do _rw[_] = {address = (Address - 1) + _, flags = gg.TYPE_BYTE} end for v, __ in ipairs(gg.getValues(_rw)) do _ = _ .. string.format("%02X", __.value & 0xFF) end return _ end Byte = {} SizeOrBuffer:gsub("..", function(x) Byte[#Byte + 1] = x _rw[#Byte] = {address = (Address - 1) + #Byte, flags = gg.TYPE_BYTE, value = x .. "h"} end) gg.setValues(_rw) end -- Usage: readedMem = rwmem(0xAABBCCDD, 128) -- Read 0xAABBCCDD with 128 size. rwmem(0xDDCCBBAA, readedMem) -- Write readedMem memory into 0xDDCCBBAA.
-
Thanks, no plan yet for x86, maybe armv8 soon.
-
View File Regview (ARMv7) Wanna debug your code ? But lazy to start remote debugging ? Use this, just put your address and ready2go ! Use this, might usefull when you want to know the caller, encrypted pointer, anything inside register. - Features: Dump Register Write Register Copy register to clipboard Jump onto register Note: Only work on 32-Bit Arm Processes. Don't forget to leave ❤, if it help you. Source: Github Submitter saiaapiz Submitted 10/02/2019 Category Tools
-
Version 1.2 (32-Bit)
4,014 downloads
Wanna debug your code ? But lazy to start remote debugging ? Use this, just put your address and ready2go ! Use this, might usefull when you want to know the caller, encrypted pointer, anything inside register. - Features: Dump Register Write Register Copy register to clipboard Jump onto register Note: Only work on 32-Bit Arm Processes. Don't forget to leave ❤, if it help you. Source: Github -
Sound like rocket science to me xD Anyway thumbs up for giving explaination
-
Actually, i've seen some apps requesting for access to devices screen. I think maybe they would do remote screenshot, then manually find for hacking tool overlay. I wish you could filter any access that required root, give user a warning like you do in gg.makeRequest. That would scripting enviroment better.
-
I wish @Enyby could add this, i think other scripter will need this too. Control GG icon overlay visibility. We need this to hide GG from getting caught from screenshot. Get 'Hide GameGuardian from game status'. Sometime user that uses script complain about game being crashed, or script has no effect on game. Drawing abilities. xD Access game data, such /data/data/<target app>.
-

84.0: Example of working with assembler / disassembler scripts - GameGuardian
saiaapiz commented on Enyby's gallery image in Video Tutorials
-
I see, There alot of work need to do. Handling, hiding, lot more thing to cover up. So i stayed with trampoline. Thank you.
-
Not watchpoint support. Backtrace ? I only can find LR (Address of current function caller.) I've created shellcode that save R0-R12, LR into stack. Then copy the stack address into my allocated region, so i can read it with script. ROM:00000000 STMFD SP!, {R0-R12,LR} ROM:00000004 LDR R0, =0xBBBBBBBB ROM:00000008 STR SP, [R0] ROM:0000000C ROM:0000000C isLocked ; CODE XREF: ROM:00000014↓j ROM:0000000C LDR R0, =0 ROM:00000010 CMP R0, #1 ROM:00000014 BNE isLocked ROM:00000018 LDMFD SP!, {R0-R12,LR} ROM:0000001C LDR PC, =0xAAAAAAAA ROM:0000001C ; --------------------------------------------------------------------------- ROM:00000020 _returnaddress DCD 0xAAAAAAAA ; DATA XREF: ROM:0000001C↑r ROM:00000024 _stackaddress DCD 0xBBBBBBBB ; DATA XREF: ROM:00000004↑r ROM:00000028 _spinlockctl DCD 0 ; DATA XREF: ROM:isLocked↑r It work like this, Firstly, i hooked an address that contain interesting info. Then, i make it jump into this shellcode, After it jump.. Shellcode will save R0-R12, LR into stack. then write the stack address at _stackaddress. this shellcode will wait for spinlock before continuing execution.
-
Yes, it look like when you setting up breakpoint with gdb, where you can view/change register in realtime. In short terms, can you add api for PTRACE_SETREGS and PTRACE_GETREGS into GG, So we can view register on any address. Nope, Chainer was used to find pointer chain.
-
Yep, u can change any value inside register.
-
I wish enyby would add this feature into GG, so i can avoid compatibility issue with shellcode. We can get dynamic pointer by viewing its register, and make cheating more advanced.
-
Idk, it just works. I didn't read hundred pages of arm documentation.
-
Let me explain this real quick. How they load offset, and calculate address ? Explanation: * PC = (Current Instruction Address + 0x8) 00000000 LDR R0, [PC, 0x1C]; Its calculated like this, R0 = (PC:00000008 + 0x1C = 00000024). Read val at 00000024 which is 0x14, then put into R0. 00000004 ADD R0, PC, R0 ; Again, R0 = (PC:0000000C + 0x14 (Offset) = 00000020) 00000008 MOV R1, #0x1234; Move 0x1234 into R1 0000000C STR R1, [R0]; Store R1:0x1234 value into R0:00000020 address. 00000010 BX LR; Jump into LR (LR is register that store address of this function caller.) 00000014 ALIGN 0x10 00000020 MyValue DCD 0x0 00000024 Offset DCD 0x14 You can find lot of information here, The ARM instruction set
-
Yep, Ida make we confuse by looking its value pointing directly to target address. Actually, true opcode look like this LDR R0, [PC, #0x4] Idk how to explain it, you can find arm opcode documentation on google. They describe how each instruction work. @Un_Known
-
Yes, you're correct. This push offset into register, then add it with PC. So PC + Offset lead to dword_36BD38 which is targeted address. R3 is address of dword_36BD38
-
0000 LDR R3, =(dword_36BD38 - 0x19D86C) -- Load offset to R3 0004 ADD R3, PC, R3 ; dword_36BD38 -- R3 = PC + Offset (R3) 0008 CMP R0, #0 -- Check if R0 value equal to 0 000C STR R0, [R3] -- Store R0 value into R3 (R3 = dword_36BD38) 0010 MOVLT R2, #0x7FFFFFFF -- If R0 value less than 0, then put (0x7FFFFFFF) 2147483647 into R2. 0014 STRLT R2, [R3] -- If R0 value less than 0, then store R2 value which is 2147483647, into R3 (R3 = dword_36BD38) Conclusion is, if R0 value less than 0.. then put 2147483647 into bss:dword_36BD38. Anyway, if you not understand about the logic. F5 hotkey may come handy.
-
View File Battleland Royal | ESP, Radar, ... Features: ○ ESP ○ Radar ○ Instant Pickup • If you like my script, Don't forget to ❤ it ! Submitter saiaapiz Submitted 06/25/2019 Category LUA scripts
- 1 reply
-
2
-
- Battleland Royale
- ESP
-
(and 2 more)
Tagged with:
-
- 1 comment
- 3 reviews
-
7
-
- Battleland Royale
- ESP
-
(and 2 more)
Tagged with: