Leaderboard
Popular Content
Showing content with the highest reputation on 08/19/2017 in all areas
-
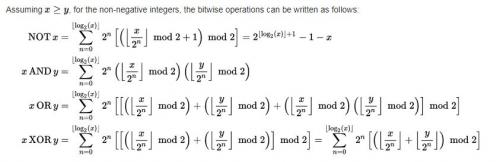
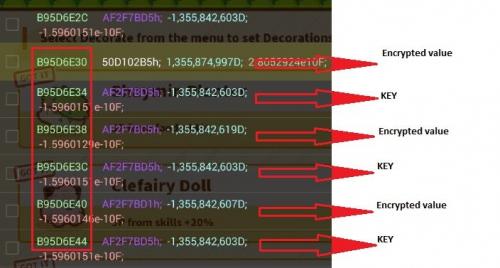
Bypassing XOR encryption in mobile games with Game Guardian In the last few months we noticed increased number of mobile games that uses some sort of encryption. Some of them are simple, like multiplying value with some random number (example: let’s say random number is 8 – in that case, 10 gold in our in-game inventory will be stored as 80 in memory). This simple kinds of encryption can’t trick anyone. But XOR encryption is different story. It is one of the simplest encryption methods, but in most cases it can’t be broken (if data and key have the same length). It is often used as a part in more advanced ciphers. But we will cover this latter. There are lot of tutorials that teach us how to bypass XOR encryption in mobile games, but most of them don’t show us process that lies behind. So before we start, we need to read some theory about the subject. If you learn this, you will be able to bypass XOR encryption with only basic memory editor, paper and pen. Of course, this is some sort of advanced tutorial – we assume that you are at least familiar with basics of memory editing. Cryptography 101 (logic for dummies) In the beginning, there was Boolean algebra. For those who haven’t overslept math and logic classes, you can skip this chapter. If you have overslept, read carefully. George Boole was mathematician, logician and philosopher who published his most famous notes in the middle of the 19th century. You probably asked yourself why are you reading about some dude who lived 100 years before ENIAC. This dude is father of all computers – every digital circuit on our planet works on his principles. For our story, it is important to notice that every algebra has own values and operations. Imagine that, in some sort of simple algebra, values are set of natural numbers from 1 to 10 [1,2,3,4,5,6,7,8,9], and only operations are addition(+), subtraction(-), multiplication(*), and division(/). From our knowledge of elementary algebra (math from school), you can tell that 1+1 =2, or 2*4=8. While elementary algebra deals with numbers, Boolean algebra use only two values – TRUEand FALSE. They are represented as 1(true) and 0(false). All operations are done on this two values. Of course, you can’t preform multiplication or subtraction on this values. We need some other operations that can be preformed on TRUE and FALSE. These operations are called bitwise operations. There are three basic operations in Boolean algebra – NOT(¬), AND (∧) and OR (∨), and they are really simple to understand. Take a look at this image, and everything will be clear. Source: Wikipedia Just kidding, forget this and let’s move on. Basic bitwise operations I know this will maybe be hard to understand, especially if this is your first time you read about logic. So I will try to make it simple. Boolean algebra (and any other logic) are made to teach us how to make correct conclusions. In elementary algebra, correct conclusion is when we write that 1+1=2. As we said, in Boolean algebra there are only two values, and we can only preform operations on them. Now imagine that we have a few true or false statements: Tom is a cat (TRUE or 1) Jerry is a mouse (TRUE or 1) Sky is green (FALSE or 0) NOT operator This is fairly simple examples. Let’s see our first operator, NOT(¬). “Tom in not a cat”, is this statement true or false? Of course, it is FALSE. Jerry is not a mouse = FALSE or 0. Sky is not green = TRUE or 1. This operator preforms logical negation on a given statement. 0 become 1, and 1 become 0. We can write it like this: ¬0 = 1 ¬1 = 0 AND operator AND(∧) operator takes two arguments, and returns TRUE only if both arguments are TRUE. Tom is a cat AND Jerry is a mouse = TRUE(1). Tom is a cat AND Sky is green = FALSE(0). You can easily remember this operator – just multiply two arguments and you have correct result. We can write it like this: 1 ∧ 1 = 1 1 ∧ 0 = 0 0 ∧ 1 = 0 0 ∧ 0 = 0 OR operator OR (∨) operator takes two arguments, and return FALSE only if both of the statements are FALSE. In every other case it returns TRUE. Tom is car OR Sky is green = TRUE(1). Sky is green OR Sky is red = FALSE(0). 1 ∨ 1 = 1 1 ∨ 0 = 1 0 ∨ 1 = 1 0 ∨ 0 = 0 Maybe you wonder why are we talking about Tom and Jerry. In computer world, everything is made in binary system. There are only two states in computer – there is current flow (1) and there isn’t current flow (0). So every information is stored in binary numeral system. Each digit (0 or 1) is called bit. Group of 8 bits are called byte. Any information can be translated into binary system. So our “tom” will be 01110100 01101111 01101101 in binary, and “sky” will be 01110011 01101011 01111001. Guess what? You can preform this bitwise operations on binary values. So, “tom” OR “sky”? 01110100 01101111 01101101 tom ∨ 01110011 01101011 01111001 sky ____________________________ 01110111 01101111 01111101 wo} If we want preform AND operator, this will be result: 01110100 01101111 01101101 tom ∧ 01110011 01101011 01111001 sky _______________________________ 01110000 01101011 01101001 pki Well, this was not very useful. But it is important to remember this, because now you will learn another bitwise operation – exclusive disjunction (exclusive OR, known as XOR). XOR (exclusive OR) bitwise operator I hope you understand these basic bitwise operators. There is also so-called “secondary operators or operations”, which can be derived from basic operators. One of these secondary operators is XOR, or exclusive OR. You will understand why is it called “exclusive OR” when you see the following table. 1 XOR 1 = 0 1 XOR 0 = 1 0 XOR 1 = 1 0 XOR 0 = 0 As you can see, if you perform XOR operation on two different values, it will return 1 or true. If values are the same, it will return 0 or false. So what is the catch? Why are XOR so special, and why is it used in cryptography? Now, look again our previous example, and you will see. From now on, we will preform XOR operation on original data (“tom” in our case) with the key (“sky” in our case). 01110100 01101111 01101101 tom XOR 01110011 01101011 01111001 sky _____________________________________ 00000111 00000100 00010100 //this can't be converted to meaningful text But what will happen if we XOR out new value (00000111 00000100 00010100) with the same key (sky or 01110011 01101011 01111001)? Let’s try it. 00000111 00000100 00010100 XOR 01110011 01101011 01111001 sky ___________________________________ 01110100 01101111 01101101 tom Right, we got our original data. But there is more -what if we don’t know the key (“sky”) 01110100 01101111 01101101 tom XOR 00000111 00000100 00010100 ___________________________________ 01110011 01101011 01111001 sky We have out original key. This is the reason why XOR operator is special. We can’t achieve this with other operators. XOR encryption in mobile games So let’s see some real world example – using XOR encryption in mobile games. Imagine that you have 1000 gold in some game. Developers implemented that all values are XOR-ed with the key 1337, and stored in memory. So look at the example. For conversion for decimal to binary you can use Windows calculator, or some online tools [BINARY TO DECIMAL CONVERTER] 0000001111101000 1000 XOR 0000010100111001 1337 _________________________ 0000011011010001 1745 This means that “1000” gold is stored as “1745” in memory. If you earn more gold (let’s say you got 1050 gold now), it will be stored in memory like this. 0000010000011010 1050 XOR 0000010100111001 1337 _________________________ 0000000100100011 291 So how we can bypass this sort of encryption? Bypassing XOR encryption with Game Guardian We already saw that: original value XOR key = encrypted value encrypted value XOR key = original value original value XOR encrypted value = key With this principle, we can bypass XOR encryption even if we don’t know that key developers used. So let’s start with practical work. If you aren’t familiar with fuzzy search, it will be useful to first read this tutorial [GAME GUARDIAN FUZZY SEARCH TUTORIAL]. We are going to use examples from previous paragraph. Our first step is to find address where the encrypted value is stored. This step is simple. First, scan for unknown starting value – this is done by selecting Fuzzy search from Game Guardian. As value type, you can choose DWORD (it was DWORD in all games that we cheated). Change the amount of gold in-game, then search for changed value. Repeat this step until only one address has left on the list. Now it is time to check if XOR encryption is used. Let’s say you got 1000 gold in game, but with fuzzy search you found value 1745. Preform XOR operation on this two values. 0000001111101000 1000 //Ingame gold XOR 0000011011010001 1745 //Value that you have found with fuzzy search _________________________ 0000010100111001 1337 //Key? --write it down Now change original value – earn or spend some gold. Let’s say you have 1050 gold now. Look at the address that you found with fuzzy search, and read the value. Again, preform XOR operation with in-game value and in-memory value. 0000010000011010 1050 //In-game value XOR 0000000100100011 291 //Value which is stored in memory _________________________ 0000010100111001 1337 //KEY!! If two keys are the same, XOR encryption is used and you have found the key. If they are not, XOR encryption is not used. Now, let’s change our gold (it was our primary goal, right?). We want 9999 gold. Again, preform XOR operation on it with key that you found (1337 in our case). 0010011100001111 9999 XOR 0000010100111001 1337 ___________________________ 0010001000110110 8758 Change the value that you found with fuzzy search – as new value set 8758. Open game again, and you should have 9999 gold. You can now cheat game using paper and pen, as we promised on the beginning. But it would be smarter if you use XOR calculator built in Game Guardian Second method to bypass XOR encryption Now, you will see the true power of Game Guardian. For this method, it is important to note that in most games, encrypted value and key are stored next to each other in memory – for DWORD type,one value occupies 4 bytes,so the key is usually 4 bytes away from encrypted value. Look at this picture. In Game Guardian, there is builtin method which automatically search for values, and XOR them with value which is X bytes away. That means that we don’t need to do fuzzy search, or calculate XOR values. Game Guardian can do it for us. Let’s get back to our previous example and imagine that encrypted value and key are 4 bytes away. If you have 1000 gold in-game, click on Known search, as type choose Dword (it can be some other types too, but it is usually dword.). As value, put in 1000X4, and click on search. In this example, first number “1000” is amount of currency that we want to change. Second part, “X4“, marks how many bytes away is the key. For dword values it can be X4,X8, X12, X16… Earn or spend some currency – let’s say that you have 900 gold now. Now input 900X4, and click on refine. Repeat previous step until you have only one address left (or few addresses if you want). Click on Edit, and as a value input 9999X4. And that’s it. Game Guardian will automatically search for encrypted values, and XOR them with key which is X bytes away. Pretty impressive feature. With this, our tutorial has finished. There will be reference links bellow, if you want to know more about this subject. Any suggestions are appreciated. Happy cheating. Reference links [Algebraic operation – Wikipedia article] [Binary numbers] [Boolean algebra] [Exclusive OR – XOR, Wikipedia] [NoFear’s tutorial – Xor search guide] [Binary to decimal online calculator]3 points
-
1 point
-
@DemiGod666. It is too late you don't have a restore that hasn't been broken. What Drake is describing here is what you should have done in the fist place to avoid this problem and what you should do in the future.1 point
-
Xiaomi path name: / storage / emulated / legacy / Android / obb Most low-level datas are stored in /sdcard/Android/data/*. But MOST of the data is stored in /data/data/*. Obb is always stored in /sdcard/Android/obb/*. That happens on most phones. I'll bet 97% of them are the same. /sdcard is INTERCHANGEABLE with /storage/emulated/legacy or /storage/emulated/0. It's not that device-specific.... Apps don't store data in external storage. Maybe a few, very few. And games won't be stored in external storage. This is not the case with phone using Adoptable Storage, in which I'm totally certain you won't use it. Checking for app data or obb won't do any good. It's useless. Why do you have to look for an app data? Different versions of an app have THE SAME data and obb label. -------- Hope that helps.1 point
-
1 point
-
1 point
-
1 point
-
1 point
-
How to use the second parameter? And one more thing. If the cheat only works with versioncode 291, how to make the script only works with that ver. Code?1 point
-
@d2dyno Thank you. At least you can try your best to add more payment methods.1 point
-
I see your point. But, a forum is for everyone even when there are premiums or VIPs. This is a place for a community, not only people who pay. VIPs can get so many privileges, but not this one. And can you tell me just a single, sizeable community forum that applies this?1 point
-
@Enyby Do you have any plans to include value freeze for scripts? Or there already is but It's just me who don't know?1 point
-
1 point
-
How to use gg.skipRestoreState? And maybe an example of using gg.getLocale @Enyby Thank you1 point
-
1 point
-
For SE Asia, Codapay is a decent option. But for other areas, MOL zGold and/or Rixty is necessary. @Enyby A survey about other countries' payment methods would be a good thing to do. @d2dyno I'm very happy if you would consider this. Thank you.1 point
-
1 point
-
@Enyby Try to utilise Codapay/Bluepay/UniPin/MOL zGold. Just like in Crisis Action SEA that got banned from GPlay because of using other payment methods.1 point
-
1 point